CyberArk uncovers significant vulnerability in Windows Hello facial recognition
The vulnerability allowed an attacker with physical access to the device to manipulate the authentication process by capturing or recreating a photo of the target’s face and subsequently plugging in a custom-made USB device to inject the spoofed images
CTech | 18:33, 15.07.21
Israel’s CyberArk Labs has published new research on a significant vulnerability in Windows Hello that allows an attacker to bypass facial recognition authentication on a target’s device. The vulnerability was assigned a CVE (base score 5.7) and has been included in the recent Microsoft Patch.
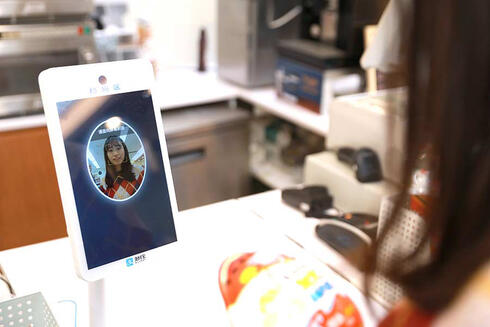
Given Windows Hello’s prevalence, over the past few months the CyberArk Labs research team has been exploring potential weaknesses in the system in hopes of strengthening biometric security overall. What resulted was the discovery of a design flaw that allows an adversary to bypass Windows Hello’s facial recognition. The vulnerability allowed an attacker with physical access to the device to manipulate the authentication process by capturing or recreating a photo of the target’s face and subsequently plugging in a custom-made USB device to inject the spoofed images to the authenticating host.
"We have no evidence that this attack has been used in the wild, but it could be used by a motivated attacker to target a researcher, scientist, journalist, activist or privileged user with sensitive IP on their device, for example," CyberArk wrote in its report authored by Security Researcher, Omer Tsarfati.
According to Microsoft, 85% of Windows 10 users use Windows Hello for passwordless authentication. As the research shows, this type of attack is highly relevant for targeted espionage – where the target is known and physical access is needed on a device.
CyberArk Labs is the research team that discovered the sophisticated GoldenSAML technique that SolarWinds attackers used to perpetrate one of the most elaborate supply chain attacks ever. According to this new research – this proof of concept on how to bypass facial recognition for authentication could have a similar impact on targeted espionage campaigns around the world.